Some Known Factual Statements About Risk Management Enterprise
Table of Contents9 Simple Techniques For Risk Management EnterpriseThe Best Guide To Risk Management Enterprise4 Easy Facts About Risk Management Enterprise DescribedAbout Risk Management EnterpriseGetting My Risk Management Enterprise To WorkAll About Risk Management Enterprise6 Simple Techniques For Risk Management Enterprise
Here are a few of its key functions that centers must know. So, have a look. Real-Time Risk Analyses and Reduction in this software program allow organizations to constantly check and evaluate dangers as they evolve. This function leverages real-time data and computerized evaluation to identify potential dangers without delay. Once risks are recognized, the software helps with instant mitigation actions.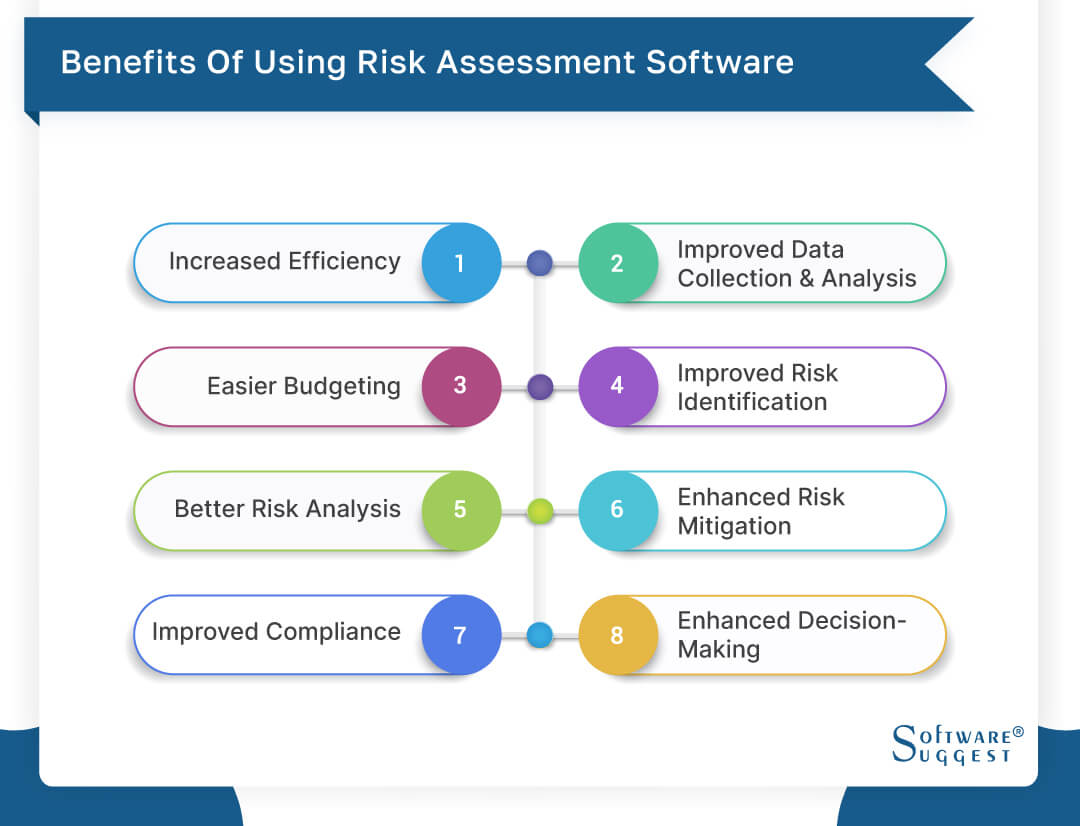
They deal with the difficulty of ongoing risk monitoring by offering tools to check threats constantly. KRIs improve safety danger oversight, guaranteeing that potential threats are recognized and taken care of efficiently.
The 6-Minute Rule for Risk Management Enterprise
IT run the risk of management is a part of business danger monitoring (ERM), designed to bring IT run the risk of in accordance with an organization's danger appetite. IT run the risk of management (ITRM) incorporates the policies, procedures and modern technology necessary to reduce dangers and susceptabilities, while maintaining compliance with applicable regulatory demands. In enhancement, ITRM seeks to limit the repercussions of damaging events, such as safety and security violations.
While ITRM frameworks supply useful support, it's very easy for IT groups to deal with "structure overload." Veronica Rose, ISACA board supervisor and an information systems auditor at Metropol Corp. Ltd., recommends making use of a mix of structures to attain the best results. For example, the ISACA Danger IT framework lines up well with the COBIT 2019 structure, Rose stated.
Venture Risk Management Software Advancement: Perks & Characteristics, Price. With technical improvements, risks are continually on the surge., organizations navigate through a regularly altering sea of risks.
All about Risk Management Enterprise
In this blog, we will certainly study the world of ERM software, exploring what it is, its advantages, functions, and so on so that you can develop one for your business. Business Threat Management (ERM) software application is the application program for preparation, routing, organizing, and controlling company tasks and streamlining danger management processes.
With ERM, organizations can make informative choices to improve the overall resilience of the business. Dedicated ERM systems are vital for organizations that routinely deal with huge amounts of delicate info and multiple stakeholders to accept tactical decisions.
: It is difficult for any type of business to undergo an extensive audit. It can be stayed clear of by making use of the ERM software program system. This system automates guideline compliance monitoring to maintain the organization secure and certified. Apart from that, it additionally logs and classifies all the files in the system making it easier for auditors to evaluate processes much faster.
The Best Strategy To Use For Risk Management Enterprise
You can also link existing software systems to the ERM through APIs or by including information by hand. Businesses can make use of ERM to review risks based upon their possible impact for far better risk administration and mitigation.: Including this feature permits individuals to obtain real-time notifications on their gadgets regarding any type of threat that might occur and its effect.
Rather, the software application permits them to set limits for different processes and send out push alerts in situation of feasible threats.: By incorporating data visualization and reporting in the custom ERM software program, companies can acquire clear understandings about threat trends and performance.: It is mandatory for companies to follow sector conformity and regulative requirements.
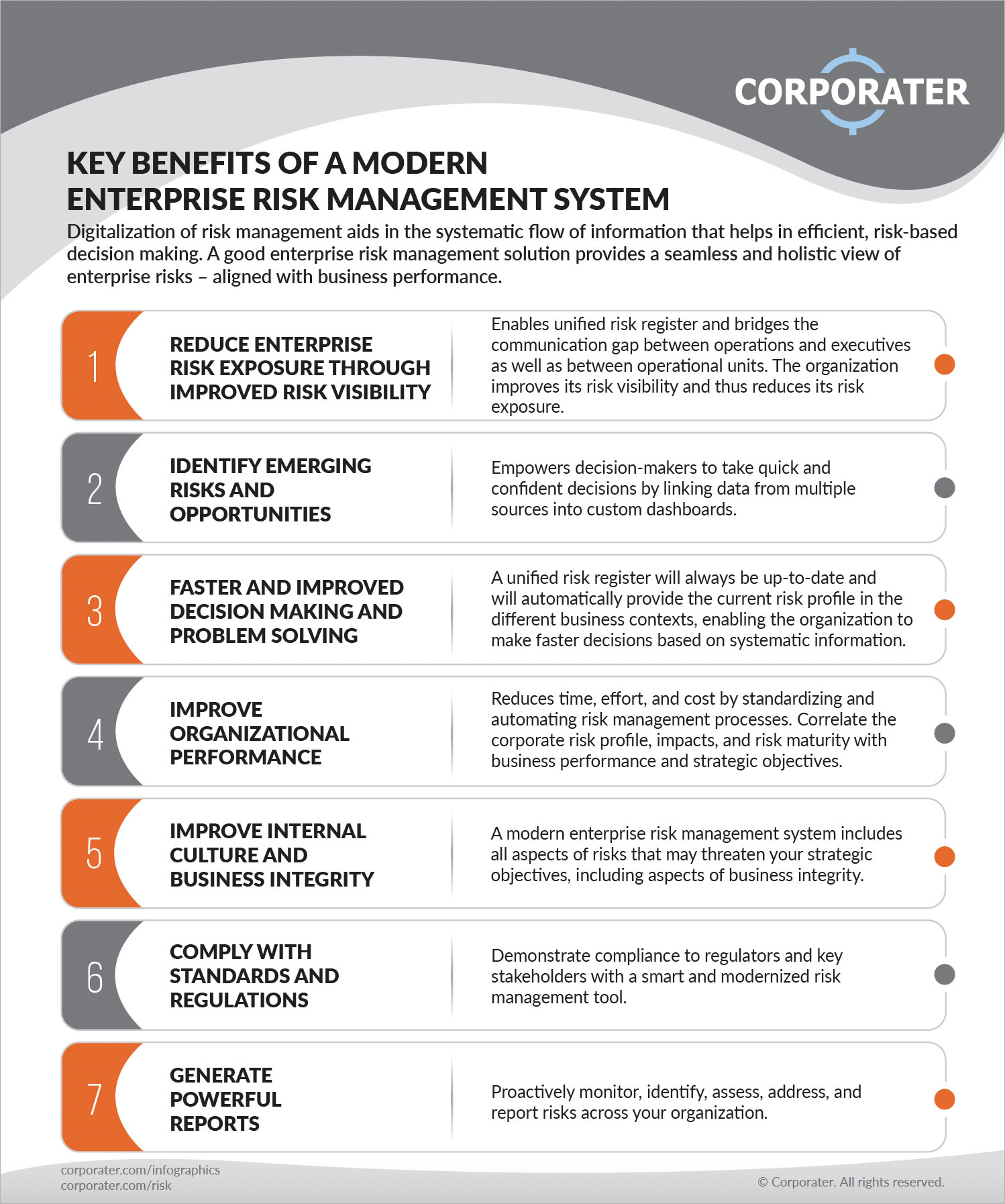
These systems make it possible for companies to execute best-practice danger administration procedures that align with sector standards, providing an effective, technology-driven technique to identifying, evaluating, and mitigating risks. This blog site explores the advantages of computerized threat management devices, the areas of threat monitoring they can automate, and the value they offer a company.
How Risk Management Enterprise can Save You Time, Stress, and Money.
Groups can set up types with the appropriate areas and quickly create various types for different danger types. These danger assessment types can be circulated for conclusion via automated process that send out notices to the relevant personnel to finish the forms online. If types are not finished by the due date, after that chaser e-mails are automatically sent by the system.
The control monitoring and control screening process can additionally be automated. Firms can utilize computerized process to send normal control test alerts and team can enter the results via on the internet types. Controls can also be monitored by the software application by establishing regulations to send signals based upon control data held in other systems and spread sheets that is drawn right into the system through API combinations.
Threat management automation software application can additionally sustain with danger reporting for all levels of the enterprise. Leaders can see reports on threat direct exposure and control performance with a range of reporting outcomes consisting of fixed records, Power BI interactive records, bowtie evaluation, and Monte Carlo simulations. The capability to pull live records at the touch of a switch removes tough information control jobs leaving risk teams with more time to analyze the data and recommend the organization on the ideal program of action.
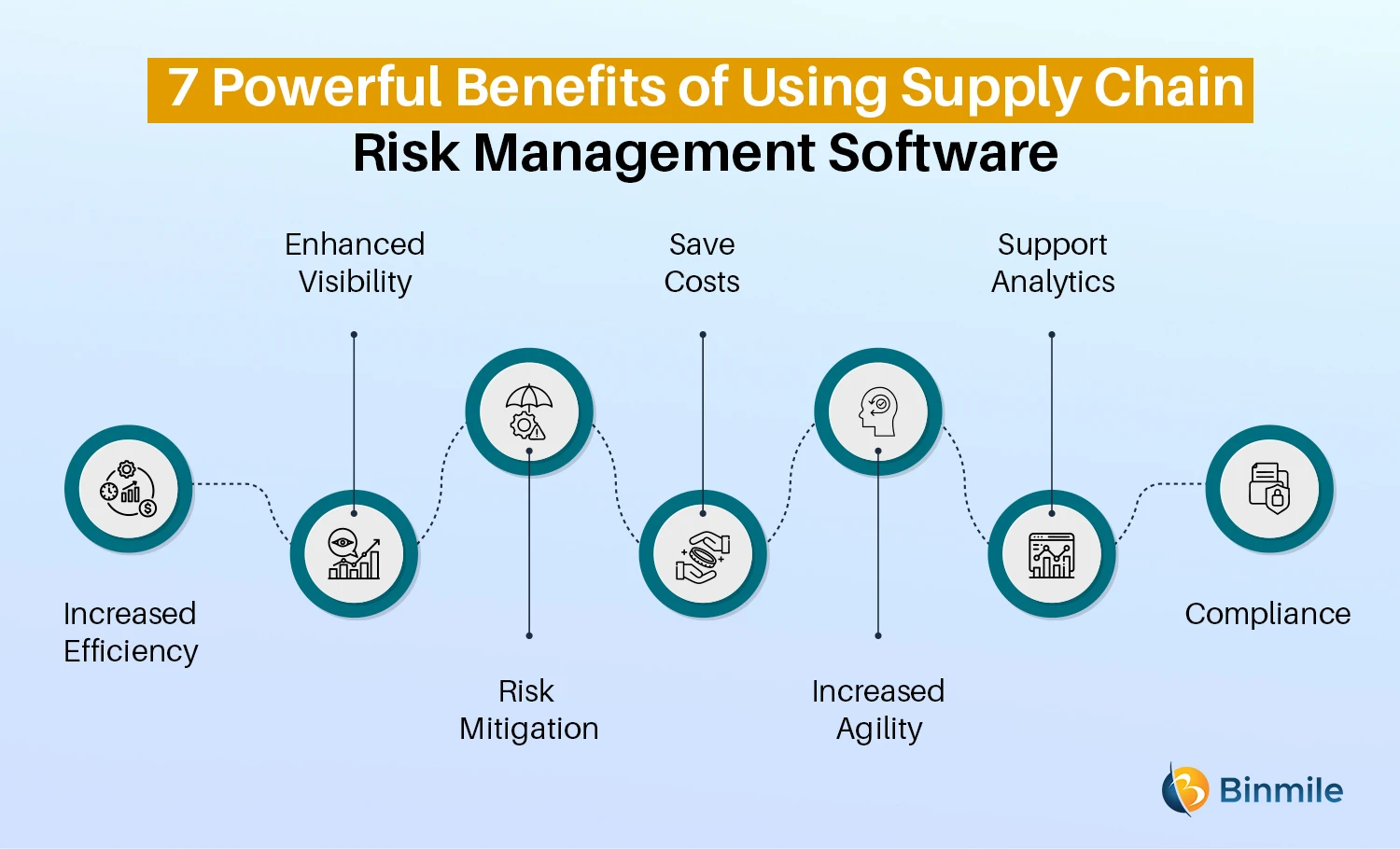
Organizations operating in competitive, fast-changing markets can not afford delays or inefficiencies in resolving prospective threats. Traditional threat monitoring utilizing manual spreadsheet-based processes, while acquainted, often lead to fragmented data, time-consuming reporting, and an enhanced chance of human mistake.
Risk Management Enterprise - The Facts
This ensures risk registers are constantly current and straightened with organizational purposes. Conformity is an additional critical chauffeur for automating threat monitoring. Criteria like ISO 31000, CPS 230 and COSO all give assistance around threat management finest methods and control structures, and automated risk monitoring devices are structured to straighten with these requirements aiding companies to fulfill most typically used risk administration standards.
Seek risk software application systems with a consents power structure to conveniently establish process for threat escalation. This capability allows you to customize the sight for every user, so they just see the data appropriate to them. Ensure the ERM software supplies individual tracking so you can see who entered what information and when.
Look for out tools that provide project danger monitoring capacities to manage your tasks and profiles and the connected dangers. The benefits of taking on danger administration automation software application prolong far beyond performance.
The Basic Principles Of Risk Management Enterprise
While the situation for automation is engaging, executing a risk administration system is not without its challenges. For one, data quality is crucial. Automated systems depend on accurate, up-to-date details to supply significant understandings. To get rid of the difficulties of threat management automation, organizations need to invest in information cleaning and governance to make sure a strong structure for implementing an automated system.
Automation in threat monitoring equips businesses to transform their approach to take the chance of and develop a more powerful foundation for the future (Risk Management Enterprise). The inquiry is no more whether to automate risk monitoring, it's how soon you can begin. To see the Riskonnect at work,
The answer usually depends on just how well threats are expected and taken care of. Job management software application offers as the navigator in the turbulent waters of project implementation, offering tools that identify and assess risks and develop strategies to reduce them check here properly. From real-time information analytics to detailed danger surveillance dashboards, these devices provide a 360-degree view of the project landscape, making it possible for project managers to make enlightened decisions that maintain their projects on the right track and within spending plan.